Technical & Political Analysis: The "Epstein Island" Call Screen Breach

WASHINGTON, D.C. — On March 27, 2026, journalists and callers using Google Pixel devices reported that the White House switchboard appeared on their screens labeled as "Epstein Island." Google has since confirmed this was the result of a "fake edit" within Google Maps that bypassed automated filters to affect the Android call identification feature. 🏛️
1. The Anatomy of the "Fake Edit"
The incident highlights a persistent vulnerability in the crowdsourced data models used by major tech platforms. ⚖️
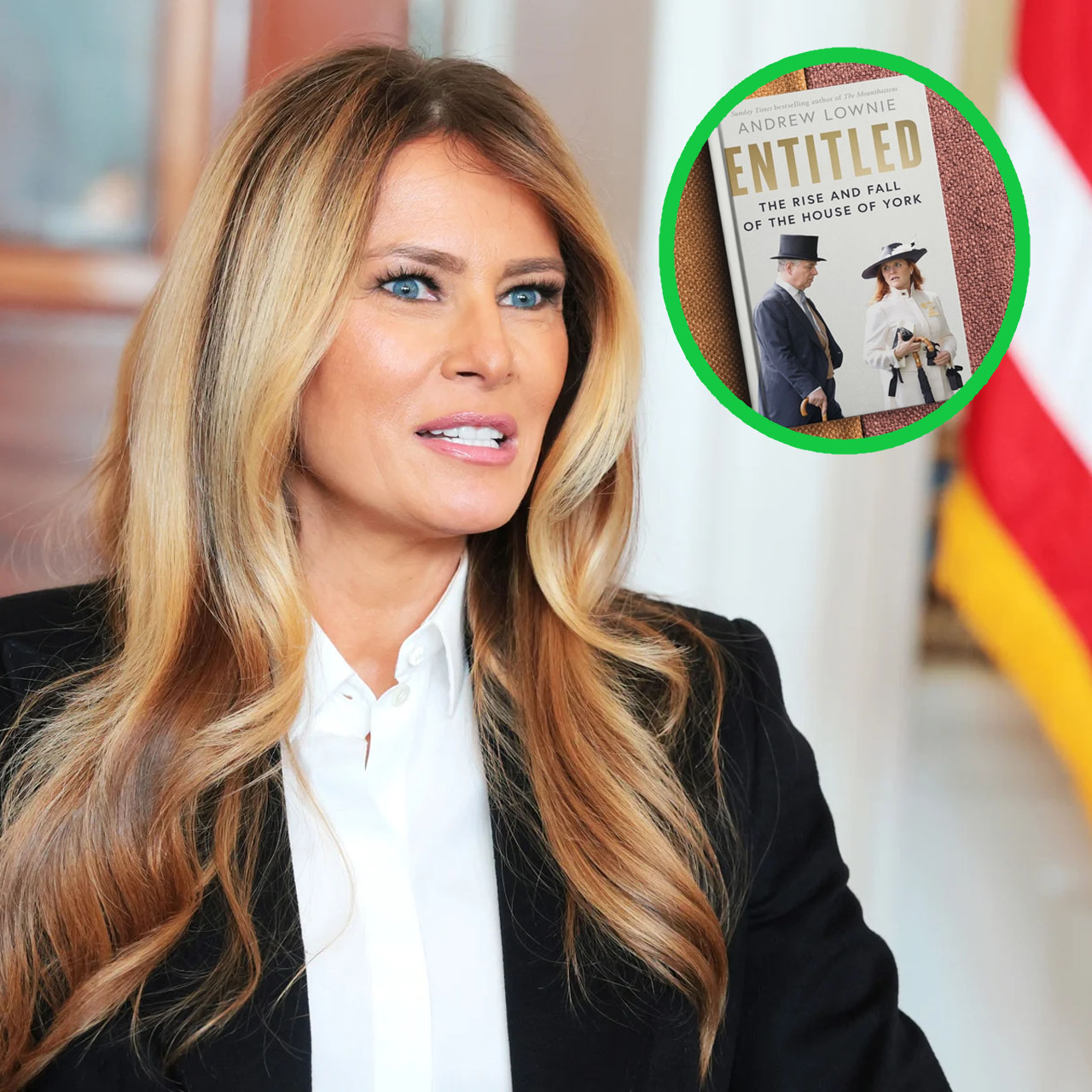
The Trigger: The breach was discovered when The Washington Post attempted to contact the White House regarding First Lady Melania Trump’s "Fostering the Future Together" AI summit on March 25. 🛡️
-
The Mechanism: Google Maps allows users to suggest "edits" to public business profiles. In this case, a malicious user successfully relabeled the White House’s primary contact number, which was then scraped by the Android Caller ID system. 📈
The Correction: Google spokesman Matthew Flegal confirmed the edit violated company policies and has been reversed. The specific user responsible has been permanently blocked from the platform. 📉
2. Historical Context of Map Pranking

This is not an isolated event; "map bombing" or prank edits have been a recurring issue for Google’s open-editing ecosystem. 🏛️
The 2024 Hong Kong Precedent: Pranksters previously relabeled several schools in Hong Kong with derogatory names, such as "Fukien Crazy Secondary School," demonstrating the scale of the vulnerability. ⚖️
External System Independence: A White House official confirmed that the labeling was strictly an external Google issue and did not involve any compromise of internal White House telecommunications or secure servers. 🛡️
The "Pixel" Factor: The issue was most prominent on Google’s own Pixel hardware, which integrates Google Maps data more deeply into the dialer interface than other Android manufacturers. 📈
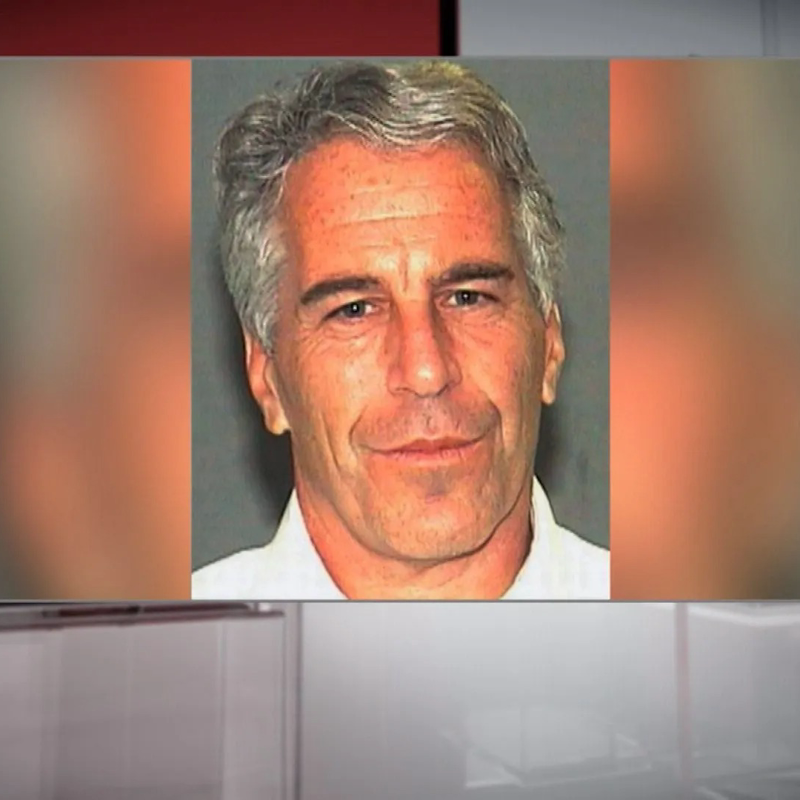
3. The Shadow of the Epstein Files in 2026

The choice of the name "Epstein Island" is a direct reflection of the heightened public sensitivity following the release of 3.5 million DOJ documents in late 2025 and early 2026. 🏛️
Narrative Saturation: The "Epstein Island" (Little St. James) moniker has become a potent political cudgel. The prank occurred just as the Epstein Files Transparency Act began surfacing new details regarding the social circles of the global elite. ⚖️
The Trump Connection: While the President has consistently maintained he had "no idea" of Epstein's crimes and banned him from Mar-a-Lago in 2006, the recent unsealing of the FBI summaries has kept the topic at the forefront of the news cycle. 🛡️
Digital Misinformation: This incident underscores how easily verified historical scandals can be weaponized through digital "pranks" to create a false sense of institutional association. 📌
SECURITY BREACH OR PERSONAL CRISIS? The Controversy Surrounding the DHS Leadership

The Department of Homeland Security (DHS) is currently facing a dual-front crisis involving both policy implementation and personal accountability. Kristi Noem, the recently appointed Secretary of DHS, finds herself at the center of a national debate following revelations regarding her husband, Bryon Noem, and potential vulnerabilities in the administration's vetting process.
1. The Allegations and Discovery
Reports originally surfacing through investigative outlets have detailed a series of online interactions involving Bryon Noem under a digital alias.
The "Jason Jackson" Profile: Allegations suggest that Mr. Noem utilized a pseudonym to engage with online content creators within specific fetish communities.
The Financial Trail: Documentation indicates payments totaling approximately $25,000 were made via digital payment platforms to various individuals over a sustained period.
The Accidental Exposure: The situation reportedly came to light not through official background checks, but via an accidental communication ("pocket dial") that led a recipient to link the private alias to the "Noem Insurance" business.
2. National Security Implications: The Blackmail Risk
Beyond the personal nature of the story, intelligence experts and media commentators have raised alarms regarding the security of the nation’s top officials.
Vetting Failures: Analysts, including former CIA officers, have pointed out that if a private citizen could uncover this information through a simple search, a hostile intelligence service could have potentially used it as leverage for blackmail.
Confirmation Questions: High-profile commentators, such as Megyn Kelly, have suggested that had this information been available during the confirmation process, the Secretary’s path to the Cabinet might have been significantly altered.
3. Policy Contradictions and the "Immigration Connection"
The story takes a complex turn with the reported involvement of an undocumented individual in the disclosure of these materials.
The "Vengeance" Narrative: Reports from Axios suggest the original tip may have come from an immigrant sex worker who sought to go public as a response to the DHS's intensified immigration enforcement and raids.
Legislative Irony: Critics have pointed to the contrast between Secretary Noem’s public stance—including support for laws restricting LGBTQ+ expressions and "drag" performances—and the private activities reported in her own household.
4. Official Response and Public Fallout
The administration and the Secretary's office have begun addressing the fallout of these revelations.
The Spokesperson's Statement: A representative for Kristi Noem stated she was "devastated" by the news, emphasizing that these activities were unknown to her.
Political Accountability: As the story evolves, the focus remains on whether a leader overseeing the nation's security apparatus can maintain public trust when a "walking blackmail target" existed within their immediate family.
THE VOTER DATA DISPUTE: Federal Access to State Records and Privacy Concerns

A significant legal and administrative conflict is unfolding between the U.S. Department of Justice (DOJ) and state governments over the centralized collection of voter registration data. The administration's plan to integrate voter files with Department of Homeland Security (DHS) databases has sparked a national debate over federal authority, data security, and the privacy of millions of Americans.
1. The Integration Plan: DOJ and the SAVE System
The core of the initiative involves the DOJ's request for comprehensive state voter lists to be processed through a DHS system known as SAVE (Systematic Alien Verification for Entitlements).
The Stated Objective: The administration maintains that this cross-referencing is necessary to identify and remove noncitizens and deceased individuals from active voter rolls.
Data Points Collected: The DOJ has requested datasets including partial Social Security numbers, driver’s license numbers, dates of birth, addresses, and in some jurisdictions like California, party affiliation and voting history.
2. Legal Challenges and Judicial Rulings
As of April 2026, the DOJ has issued demands to 48 states and the District of Columbia, leading to a wave of litigation.
The Resistance: At least 30 states have faced federal lawsuits for refusing to comply with the data requests.
Judicial Pushback: Federal judges in California, Oregon, and Michigan have recently ruled against the DOJ, stating that the federal government lacks the statutory authority to maintain a centralized national database of state voter records.
Privacy Officer Resignation: The debate was further intensified by the recent resignation of the Civil Rights Division’s privacy officer, who reportedly stepped down due to concerns over the program's implications for individual rights.

3. Current Implementation Status
While many states are fighting the demands, approximately 12 states have already transferred their voter data to federal custody.
Participating States: Alaska, Arkansas, Indiana, Louisiana, Mississippi, Nebraska, Ohio, Oklahoma, South Dakota, Tennessee, Texas, and Wyoming.
Administrative Agreements: Under the current framework, states that provide data enter into agreements allowing the DOJ to flag "ineligible" voters, with a mandate for removal within a 45-day window.
4. The Privacy and Oversight Debate
Organizations such as the Electronic Privacy Information Center (EPIC) have raised alarms regarding the security of connecting voter files directly to immigration enforcement databases.
Security Concerns: Analysts warn that centralizing such sensitive information creates a significant target for data breaches and potential misuse.
The "Fraud" Narrative vs. Data Reality: While the administration cites election integrity as the primary driver, civil rights advocates point to the historical rarity of voter fraud, arguing that the focus should remain on protecting the privacy and access of legitimate voters.
As the 2026 election cycle approaches, the outcome of these ongoing court battles will determine the boundary between federal oversight and state control over election administration.